|
|||||
|
After the first launch of Secure Office .NET, you can see the Administrator's window and the tray icon. You can minimize or close the window, but the program will continue to work. If you want to exit the program, use the tray icon near the clock to exit or click "Close the program" link in the main window. You have to start the system service "Secure Office.Net Loader" to upload the log files to the SQL database. The service starts automatically with Windows. 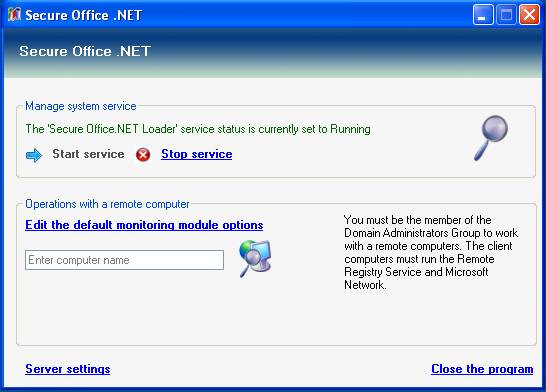 Buttons: .png) Search for a computer in the Network Neighborhood.
Search for a computer in the Network Neighborhood. View the recorded users'
logs. View the recorded users'
logs.When you enter the network computer name, two additional links appear. 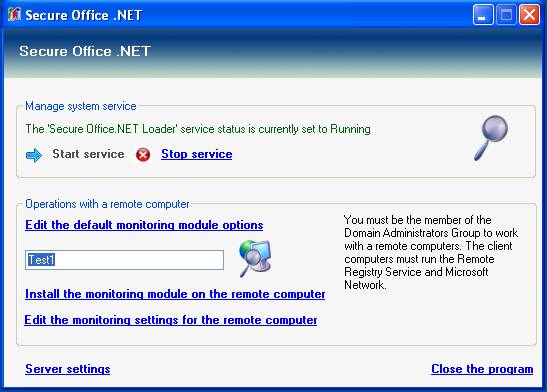 Select "Install the monitoring module on the remote computer" to start the remote installation of the monitoring module. Don't forget to configure the remote module's options before the remote installation. The monitoring of the remote computer will start with a next user logon. After the remote installation you can edit the remote module's options at any time. The remote installation uses the Windows Remote Registry Service, so make sure it is enabled on the target PC. After the initial installation of Secure Office .NET: 1. Configure administrator's module options Click Server Settings. Set the path for the logs directory on the server, and the number of days to store the logs in the database. Remember: more days you store the logs - more disc space and database resources they require. Also there is a "Run at startup" option and "Access password" option. That password protects the access to the administrator's module. 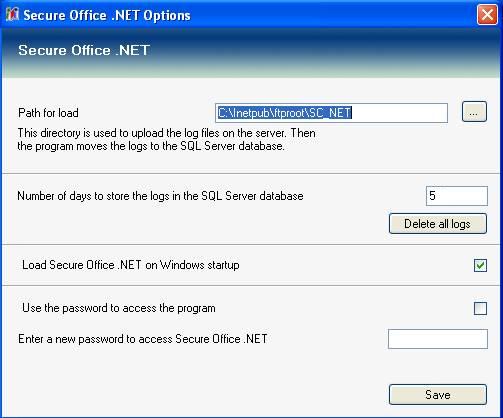 2. Configure the default settings for remote monitoring modules. Use Secure Office .NET Configuration Wizard to edit and save the default monitoring options. The default monitoring options are used for every new remote monitoring module. 3. Install the remote monitoring modules on the network computers For beginning, it's recommended to install the remote monitoring module on one network computer to ensure it will work correctly. Then install the monitoring modules on all other network computers you want to monitor. |



